Data Loss Prevention (DLP)
Privileged Access Management Buyers' Guide
Security breaches show no signs of slowing, and credential theft headlines are the number one attack...
2022 Cost of Insider Threats: Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...

Your Path to Zero Trust
In a business world without perimeters and dominated by remote work, finding a balance between easy collaboration...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...
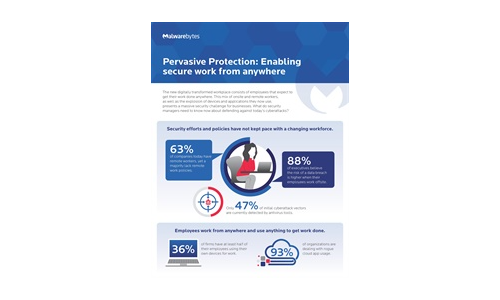
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.