Secrets Management
5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...

UK National Cyber Strategy: BAE Systems Response
The new UK National Cyber Strategy represents a key moment in cyber policy and ambitions. Here, we reflect...
Cloud Cyber Resilience Report
After a dynamic year for cloud native apps, Tenable has compiled a report focusing on trends and recommendations...
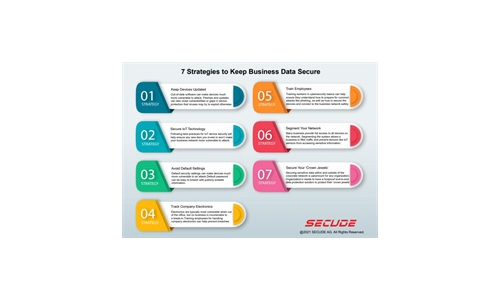
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...

CyberArk 2022 Identity Security Threat Landscape Report
A global report from CyberArk which shows that 79% of senior security professionals say that cybersecurity...

First steps to data provisioning maturity
An organization's deepest insights are often derived from sensitive data. Responsible organizations know...
Supporting Success in Federal Government Healthcare
Automation, technology expertise, and a dedicated partnering philosophy are key to driving success. And...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

