Latest Whitepapers
The Five Nastiest Security Mistakes Exposing Public Cloud Infrastructure
Public cloud infrastructure has become a critical asset to enterprises that compete on innovation. Protecting...
BNPL Consumer Research Report 2022
Buy Now, Pay Later (BNPL) financing has become hugely popular over the last few years. However, as BNPL...
The Definitive Guide to Data Security Posture Management (DPSM)
DSPM charts a modern path for understanding everything that affects the security posture of your data....

Why Security Needs An Application-Centric Lens
An application-centric view of security should be based on four critical security capabilities. We discuss...
Reduce Alert Fatigue in Your IT Environment
Security teams are tasked with managing a huge volume of alert logs, and this noise can overwhelm any...

Top Threat Detections Seen Across Healthcare Organizations
We consider the relationship between Healthcare and Cybersecurity today. How can healthcare security...
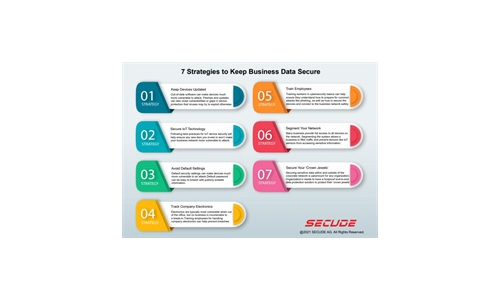
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
Zero Trust Privilege for dummies
Cyber breaches are bigger and worse than ever. Hardly a day goes by without headlines about some new...
The Perimeter’s Gone. Can Your Security Handle It?
Organizations need to shift their security strategy to secure the new ways work gets done. That takes...

Strengthening Critical Infrastructure Security
Advances to critical infrastructure technology is opening the door to threat actors and cyber attacks...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.