Latest Whitepapers
Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another security breach. Ponemon Institute has found that the typical...
CIO Priorities: Forcing Business to Evolve
It's apparent now that the forces pushing for businesses to embrace technology to modernization are unstoppable....

Raising the Bar for Web App and API Security
Most Web Application and API Security Isn't Enough Securing the web applications and APIs that underpin...
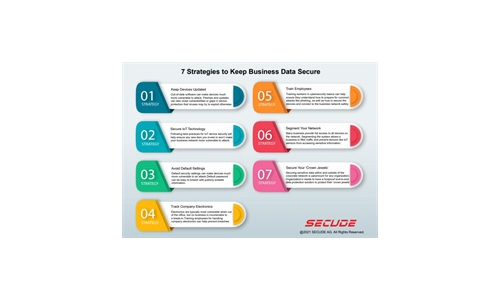
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
Insider Risk: Shifting the Focus With Zero Trust
Zero Trust assumes no entity is implicitly trusted regardless of whether it is internal or external to...

Forbes Study - CIO 2025
Important as the cloud already is, next-generation cloud and multicloud are expected to play even more...
What is Zero Trust? (Really)
Over the last decade, cybersecurity has been focused on the challenge of securing increasingly vulnerable...

Understanding Why Multi-Signal MDR Matters
MDR providers can only detect and respond to what they can see. A multi-signal approach is paramount...
Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...

The Evolving Cybersecurity Landscape
Transformation to the cloud is no longer a choice but a business necessity. Whereas before the transition...
Sophos 2022 Threat Report
Interrelated threats target an interdependent world. We believe that shifting the timescale of attack...
Collective Defense: A radar-like view of cyber threats
IronNet is committed to answering the World Economic Forum's call to action for collaborative cyber defense....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.