Data Security
Proofpoint Information and Cloud Security Platform
The Proofpoint Information and Cloud Security platform combines many of our products to address secure...

First steps to data provisioning maturity
An organization's deepest insights are often derived from sensitive data. Responsible organizations know...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...
Cloud Data Security 2023 Report by ESG, a division of TechTarget
…More than half (59%) of respondents believe that more than 30% of their organization's sensitive data...
Protecting your content against cyber threats and data loss
How the Content Cloud safeguards your most valuable information Your business runs on content — but...

CIO Essential Guidance: CISO Security Threat landscape
After a year that saw the largest and fastest transformation in work patterns in history, security teams...
Pain & Progress: Cybersecurity and Business Risk Study
Despite their best efforts and investments, some organisations still experience difficulty as a result...
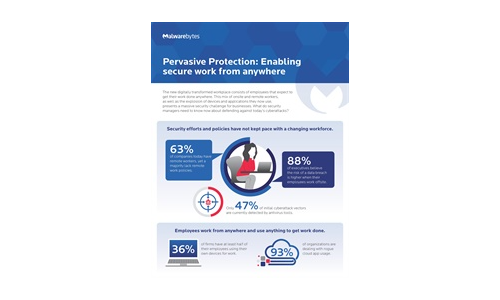
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

UK National Cyber Strategy: BAE Systems Response
The new UK National Cyber Strategy represents a key moment in cyber policy and ambitions. Here, we reflect...
6 Misconceptions about Collective Defense for Cybersecurity
Collective Defense uses collaboration and threat information sharing in new and powerful ways to reduce...
Protect K-12 Schools from Cyberattacks with Active Breach Protection
Ransomware is not just another buzzword. It is a very real threat to educational institutions of all...
Modern Networking for the Borderless Enterprise
5 Ways Top Organizations Are Optimising Networking at the Edge. Enterprises are growing more dispersed...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.