Endpoint Protection

Multi-Vector Protection
Educating users is an undeniably effective way to protect them from phishing and other malware, but it...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...
Back to the Basics: Cyber Hygiene Starts with Asset Management
The challenge: managing millions of dynamic, distributed and diverse assets while maintaining high standards...
6-Step Cybersecurity Starter Guide for SMBs
Computers and the internet bring many benefits to small businesses, but this technology is not without...
Build or Buy? Answering the Eternal Technology Question
The eternal technology question seems to be, “Build or buy?” It is usually posed when a technology...
The Complete Guide to Enterprise Ransomware Protection
The SentinelOne Complete Ransomware Guide will help you understand, plan for, respond to and protect...

Realizing The Devops Vision In Embedded Systems
Markets demand ever more complex systems and faster development cycles. Meanwhile, there is a shortage...

Building the foundation of a mature threat hunting program
Many organizations, especially large global enterprises, don't always have the best visibility into how...
The Perimeter’s Gone. Can Your Security Handle It?
Organizations need to shift their security strategy to secure the new ways work gets done. That takes...
Social Engineering Handbook: How to Take the Right Action
The aim of this handbook is to help introduce social engineering and its risks to every employee in the...
Using MITRE ATT&CK™ in Threat Hunting and Detection
Threat hunting is the process of proactively searching for malware or attackers that reside on your network...
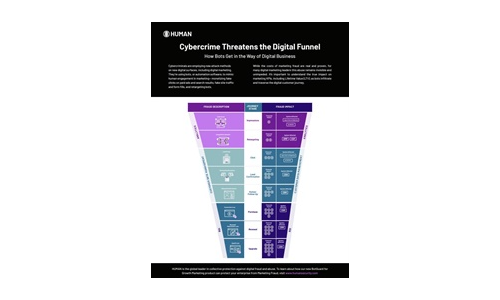
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.