Email Security
Confronting the NEW WAVE OF CYBERATTACKS
Like the virus responsible for the worldwide pandemic, email-based cyber threats continued to mutate...

Cloud Adoption and Risk Report
The recent work from home mandate has dramatically changed how we live and work. Organisations are getting...

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...
5 Uncomfortable Truths About Phishing Defense
When over 90% of breaches start as phishing emails threats that email gateways miss and other defenses...
Reduce Alert Fatigue in Your IT Environment
Security teams are tasked with managing a huge volume of alert logs, and this noise can overwhelm any...
Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...
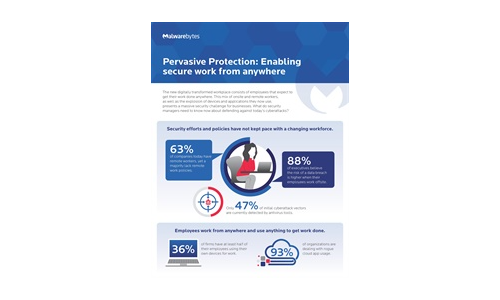
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

The Cost of ‘Good Enough’ Security ebook
Investing in cybersecurity technologies is one strategy for reducing cyber risk. But how can you be confident...

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...
Enhancing Microsoft Security with HelpSystems Email Security
Learn how HelpSystems Email Security can enhance Microsoft 365. Microsoft 365 offers tiers of security...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.