Email Security

Ransomware Case Studies
Ransomware is a simple name for a complex collection of security threats. Attacks can be short and brutal,...
Confronting the NEW WAVE OF CYBERATTACKS
Like the virus responsible for the worldwide pandemic, email-based cyber threats continued to mutate...
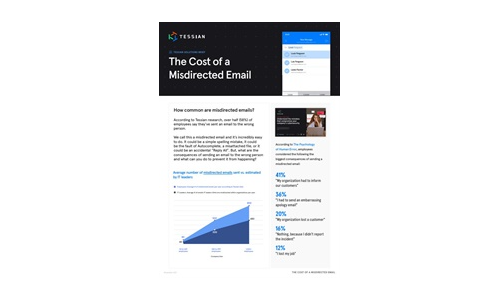
What is the Cost of a Misdirected Email?
The average number of misdirected emails is almost always higher than IT leaders estimate, making it...
A Guide for SMBs: Can I really become “less hackable”?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...
State of Ransomware Readiness 2022
Ransomware has become one of the primary threats to organizations of all types over the past few years....

Mitigating Information Security Risks in Microsoft 365
Microsoft 365 offers multiple tiers of capabilities that all leverage the cloud to enable professionals...
Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...
Essential How-To Guide: Prevent Accidental Emailing
NO ORGANIZATION IS IMMUNE TO HUMAN ERROR In this e-book you'll get a closer look at data breaches and...

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...
Drive Real Behaviour Change
Cybersecurity awareness training is one of the most important things you can do to secure your organisation....

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.