Network Security

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...

UK National Cyber Strategy: BAE Systems Response
The new UK National Cyber Strategy represents a key moment in cyber policy and ambitions. Here, we reflect...
Zero Trust Privilege for dummies
Cyber breaches are bigger and worse than ever. Hardly a day goes by without headlines about some new...
Building Your MSP Security Offerings
As a managed service provider (MSP), your customers already expect you to keep their networks secure....
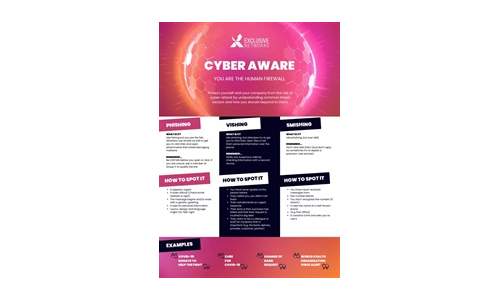
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...

The Future of Cybersecurity For Today’s Cloud- and Mobile-First World
Today, there's a sharp focus on embracing zero trust as the future of cybersecurity. With apps, users,...
An Overview of Cato Data Loss Prevention (DLP)
ata is the most valuable asset a modern enterprise has. The evolving threat landscape and shift to cloud...

The Top Questions to Ask in Your SASE RFP
Moving to a cloud-delivered architecture can be daunting. It is essential to find a SASE provider who...
Using MITRE ATT&CK™ in Threat Hunting and Detection
Threat hunting is the process of proactively searching for malware or attackers that reside on your network...
Social Engineering Handbook: How to Take the Right Action
The aim of this handbook is to help introduce social engineering and its risks to every employee in the...

7 Metrics to Measure the Effectiveness of Your Security Operations
You can't improve what you don't measure. To mature your security operations center (SOC) and security...

The 10 Tenets of an Effective SASE Solution
As cloud adoption grows, cloud-enabled organizations are experiencing an influx of new security requirements....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



